As digital interactions increasingly move onto decentralized networks, the question of identity has become one of the most pressing challenges in Web3. Traditional identity systems are built around centralized authorities that issue, verify, and store user data. In contrast, decentralized ecosystems require trustless, privacy-preserving, and user-controlled identity frameworks. Web3 identity tools aim to solve this tension by enabling decentralized user profiles that are secure, interoperable, and resilient.
TLDR: Web3 identity tools allow users to control and manage their digital identities without relying on centralized platforms. These systems use blockchain technology, decentralized identifiers, and verifiable credentials to create secure and portable profiles. They enhance privacy, reduce reliance on intermediaries, and enable seamless interaction across decentralized applications. While challenges remain, Web3 identity frameworks are rapidly maturing and reshaping digital trust online.
The Shift from Centralized to Decentralized Identity
Traditional digital identity models depend on centralized databases managed by corporations or governments. Every time users log in to a platform, verify their identity, or share personal data, they place trust in a central authority. This creates several risks:
- Data breaches due to centralized storage
- Limited user control over personal information
- Fragmented digital identities across multiple platforms
- Vendor lock-in and restricted interoperability
Web3 identity tools aim to address these problems by decentralizing identity management. Instead of a company owning your profile, you own and control it through cryptographic keys stored in digital wallets. Identity becomes portable, composable, and resistant to unilateral control.

This fundamental shift redefines digital trust. Rather than trusting an intermediary, users and platforms rely on cryptographic proofs anchored to distributed networks.
Core Components of Web3 Identity Systems
Decentralized identity systems are built on several foundational technologies. Understanding these components is essential for evaluating current and emerging tools.
1. Decentralized Identifiers (DIDs)
Decentralized Identifiers are unique, blockchain-anchored identifiers that are created and controlled by users. Unlike email addresses or usernames issued by corporations, DIDs are:
- Globally unique
- Cryptographically verifiable
- Not dependent on centralized registrars
DIDs allow users to authenticate digitally without disclosing unnecessary personal information, supporting privacy-first verification.
2. Verifiable Credentials (VCs)
Verifiable credentials are digitally signed attestations issued by trusted entities. They function similarly to physical documents such as diplomas or licenses but exist in tamper-proof digital form.
For example, a university could issue a verifiable credential confirming a degree. A user can later present cryptographic proof of the credential without exposing unrelated personal data.
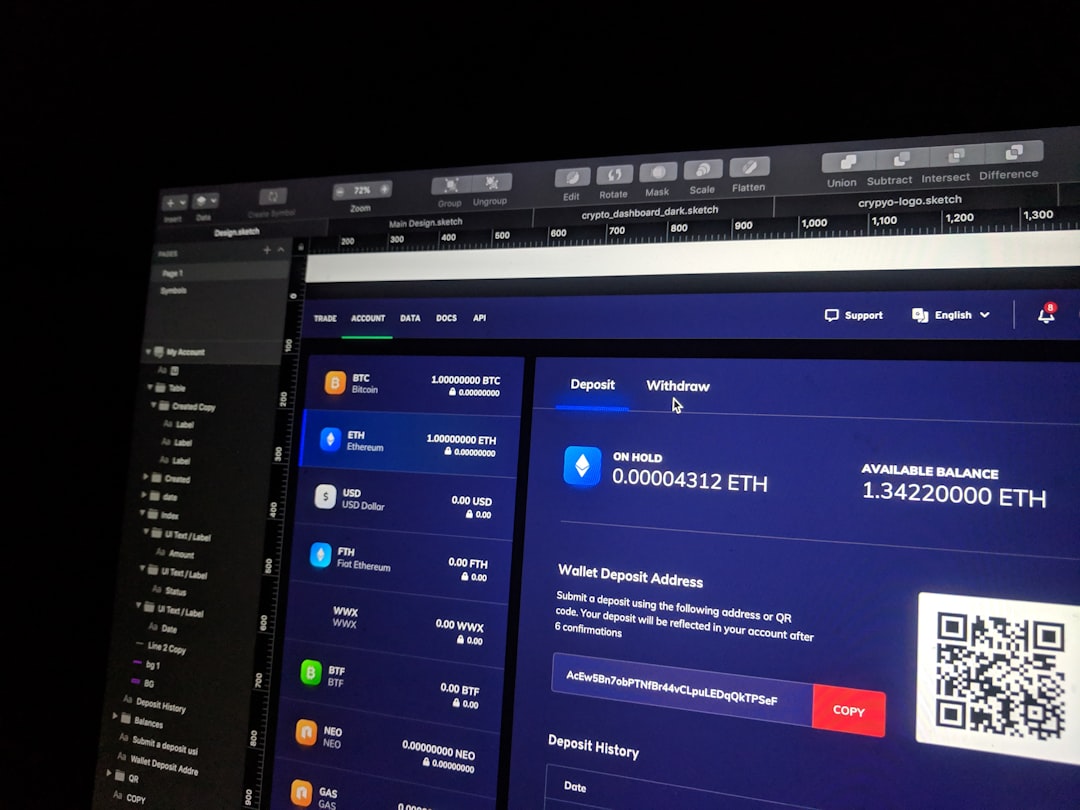
3. Digital Wallets
Digital wallets serve as secure containers for keys, identifiers, and credentials. They enable:
- Self-sovereign authentication
- Secure credential storage
- Selective disclosure of information
Wallet-based identity empowers users to decide when, where, and how their data is shared.
4. Blockchain Infrastructure
Blockchains function as decentralized registries that anchor identity proofs. They ensure immutability, auditability, and resilience against tampering. Importantly, sensitive data is typically stored off-chain, while proofs and references are recorded on-chain to preserve privacy and efficiency.
How Decentralized User Profiles Work
A decentralized user profile differs fundamentally from a traditional online account. Rather than existing within a single platform’s database, it operates as a portable identity layer that can be used across multiple applications.
A typical flow may involve:
- A user creates a decentralized identifier through their wallet.
- Trusted issuers provide verifiable credentials tied to that identifier.
- The user stores these credentials securely.
- When accessing a decentralized application, the user signs a cryptographic challenge to authenticate.
- If required, the user shares specific proofs rather than full documents.
This approach introduces selective disclosure, meaning users can reveal only the data necessary for a specific transaction. For example, proving they are over 18 without revealing their exact birthdate.
Key Benefits of Web3 Identity Tools
1. Self-Sovereignty
Users retain ownership and control over their identity credentials. No centralized entity can revoke access arbitrarily or monetize personal data without consent.
2. Privacy by Design
Modern decentralized identity tools integrate advanced cryptographic methods such as zero-knowledge proofs. These enable verification without full data disclosure, significantly reducing exposure risks.
3. Interoperability
Standardized identity protocols allow decentralized profiles to function across multiple ecosystems. Instead of creating separate accounts for each service, users maintain a unified identity layer that travels with them.
4. Security Improvements
With no central honeypot database, the attack surface shifts. While users must safeguard their private keys, the systemic risk of large-scale identity breaches decreases.
5. Reduced Fraud
Verifiable, cryptographically signed credentials make it significantly harder to forge qualifications or impersonate others. Authenticity can be verified mathematically rather than relying on manual checks.
Use Cases Driving Adoption
Web3 identity tools are advancing across multiple sectors, demonstrating practical value beyond theoretical frameworks.
Decentralized Finance (DeFi)
Identity layers can support compliance requirements while maintaining user privacy. For example, a user may prove eligibility without publicly revealing financial details.
Decentralized Autonomous Organizations (DAOs)
Reputation systems built on decentralized profiles allow governance mechanisms to incorporate verifiable participation history, contribution records, and voting rights.
Education and Certification
Institutions can issue tamper-proof digital credentials that remain permanently verifiable. Employers can validate achievements instantly without relying on manual verification processes.
Healthcare
Patients can manage access permissions to medical records while maintaining an auditable history of data sharing.
Image not found in postmetaChallenges and Limitations
Despite their promise, decentralized identity tools are not without obstacles. Mature implementation requires thoughtful governance, usability optimization, and regulatory alignment.
User Experience Complexity
Managing private keys and cryptographic credentials can be daunting for non-technical users. Lost keys may result in permanent identity loss unless recovery mechanisms are carefully designed.
Standardization Gaps
Although significant progress has been made toward interoperable standards, fragmentation across ecosystems remains a challenge.
Regulatory Uncertainty
Governments are still determining how decentralized identity frameworks fit within existing legal and compliance structures. Balancing privacy with regulatory obligations requires strategic collaboration.
Scalability Considerations
Public blockchains must handle increasing identity-related transactions without compromising performance or costs.
Trust Frameworks and Governance
Decentralized identity does not eliminate trust; it redistributes it. Trust frameworks define which entities can issue credentials and under what standards they operate. Clear governance policies are essential to ensure the credibility and reliability of identity ecosystems.
Well-designed systems generally feature:
- Transparent issuance criteria
- Open technical standards
- Revocation and status-check mechanisms
- Auditability without compromising privacy
This structured approach enables decentralized profiles to function reliably in high-stakes environments such as finance, public services, and enterprise workflows.
The Road Ahead
Web3 identity tools are transitioning from experimental implementations to infrastructure-level components of decentralized networks. As wallet interfaces become more intuitive and recovery mechanisms more robust, mainstream adoption barriers are likely to diminish.
Future developments may include:
- Biometric-secured wallet integrations
- Advanced zero-knowledge proof applications
- Cross-chain identity interoperability
- Greater enterprise and government participation
Ultimately, decentralized user profiles represent a broader reimagining of digital identity. Instead of being passive subjects of platform policies, individuals become active custodians of their data and credentials.
Conclusion
Web3 identity tools provide a serious and structurally sound response to the limitations of centralized identity management. By leveraging decentralized identifiers, verifiable credentials, and cryptographic authentication, they establish a framework where users retain ownership and platforms gain reliable verification mechanisms.
While challenges related to scalability, usability, and regulation remain, progress in standards and infrastructure continues to strengthen the viability of decentralized user profiles. As digital environments evolve, identity will increasingly serve as a foundational trust layer rather than a platform-bound asset. In this emerging paradigm, decentralized identity tools are not merely enhancements—they are essential building blocks for a more secure, interoperable, and privacy-respecting digital ecosystem.